I'm Kelvin Magora — a cybersecurity professional with a strong academic foundation and proven impact across vulnerability management, SOC operations, detection engineering, and cloud security.
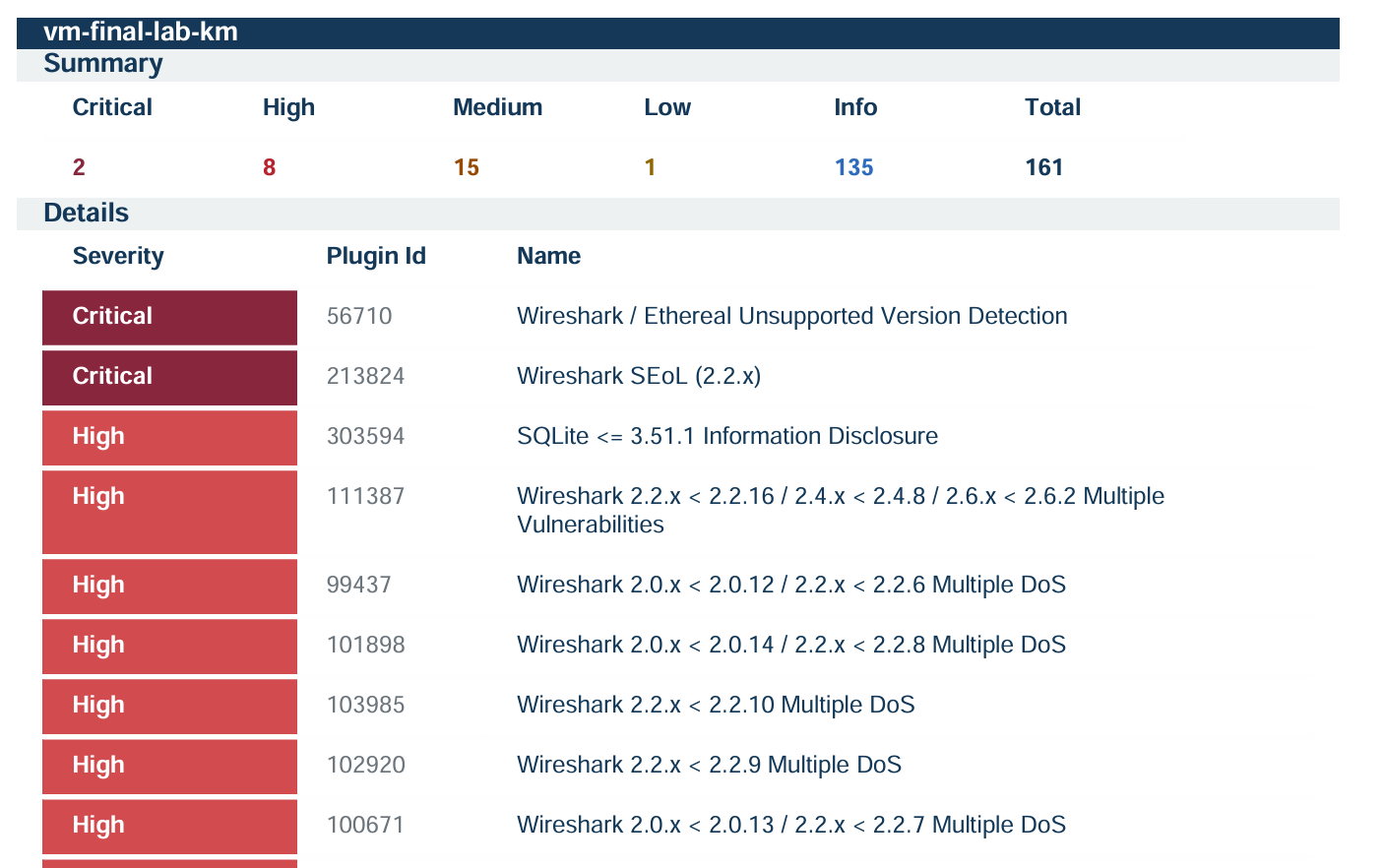
I've delivered results that matter to organisations: 100% elimination of critical vulnerabilities for a server team, reduced brute force incidents to zero through smart infrastructure controls, and improved threat visibility for over 1,000 users monthly at a financial institution.
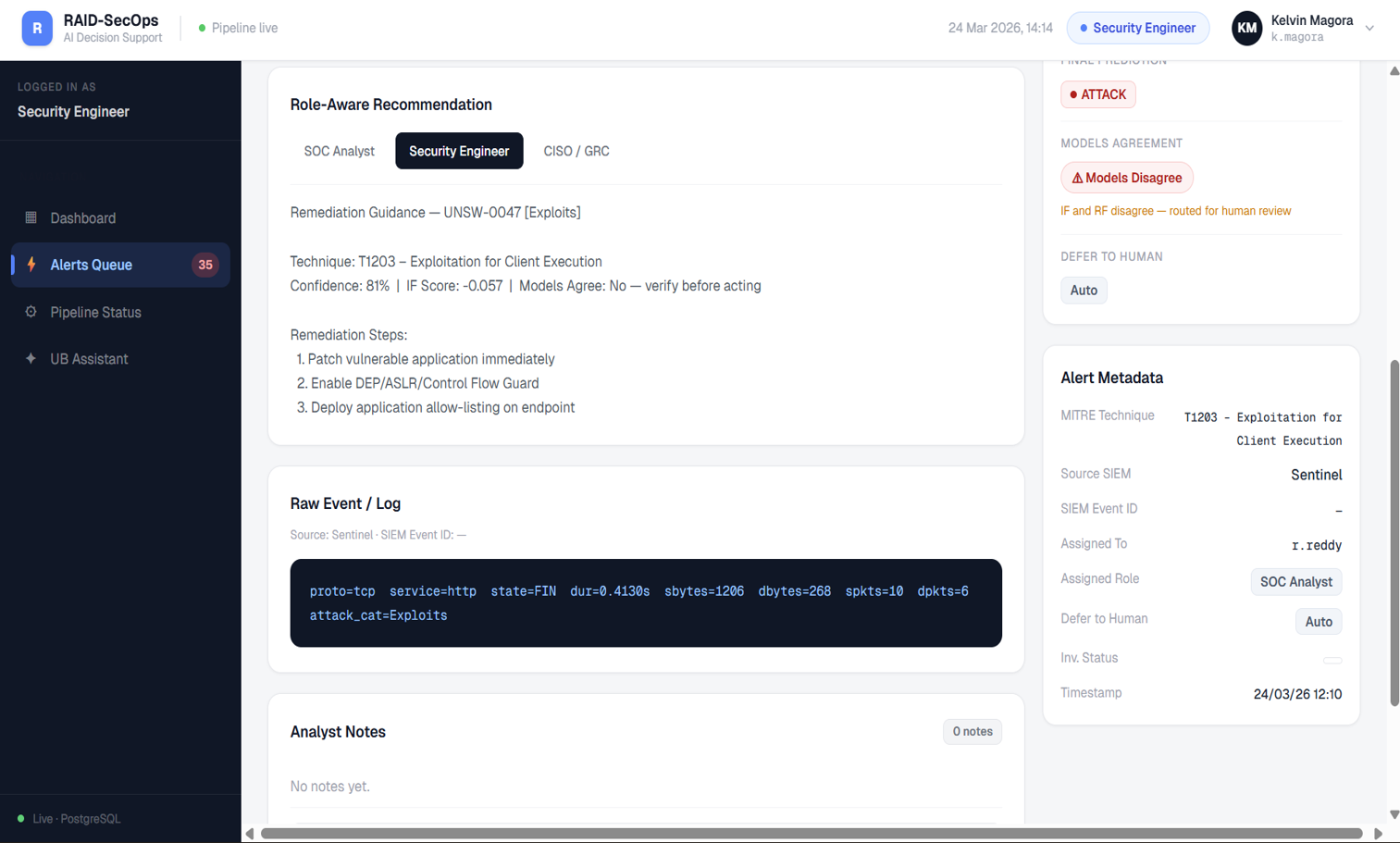
My work bridges offensive and defensive security — I understand attack paths, and I use that knowledge to build defences that actually hold. Whether engineering detection rules in Microsoft Sentinel, hunting threats via EDR, or assessing cloud posture against CIS benchmarks, I bring rigour and business context to every engagement.
Currently completing my MSc in Cybersecurity at Yeshiva University, with two published research papers on cloud forensics and AI-driven threats in healthcare. I'm looking for roles where security is treated as a strategic enabler — not just a compliance function.


 t
t



